So, my CCNP studies slipped onto the back burner recently as I focussed on passing my JNCIA-Junos cert, so it’s time to pick up where my last post left off and move on from a basic EIGRP config to some more advanced stuff.
We know that two EIGRP routers will become neighbours if they have the same AS number, the K values match and they are on the same data link. This is great, but suppose the bad guys were able to connect their own router to the same data link and then cause EIGRP routing mayhem – how do we stop this??? You guessed it – Authentication, and here’s how we do it:
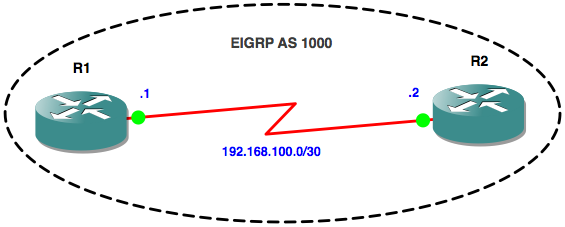
Here’s our simple topology from last time:
Let’s just verify that all is good and we have happy neighbours:
R1#sh ip eigrp nei
IP-EIGRP neighbors for process 1000
H Address Interface Hold Uptime SRTT RTO Q Seq
(sec) (ms) Cnt Num
0 192.168.100.2 Se0/0 10 00:20:48 8 200 0 4
R1#sh run | s key key chain EIGRPAS1000 key 1 key-string password1 accept-lifetime 00:00:00 Jun 1 2013 00:00:00 Jun 30 2013 send-lifetime 00:00:00 Jun 1 2013 00:00:00 Jun 30 2013 key 2 key-string password2 accept-lifetime 00:00:00 Jun 29 2013 00:00:00 Jul 31 2013 send-lifetime 00:00:00 Jun 29 2013 00:00:00 Jul 31 2013
R1(config)#interface Serial0/0 R1(config-if)#ip authentication mode eigrp 1000 md5 R1(config-if)#ip authentication key-chain eigrp 1000 EIGRPAS1000
Notice that immediately the adjacency goes down as we haven’t configured the interface on R2 yet:
Jun 5 20:40:11.767: %DUAL-5-NBRCHANGE: IP-EIGRP(0) 1000: Neighbor 192.168.100.2 (Serial0/0) is down: authentication mode changed
Next, we configure R2’s interface:
R2(config)#interface Serial0/0 R2(config-if)# ip authentication mode eigrp 1000 md5 R2(config-if)# ip authentication key-chain eigrp 1000 EIGRPAS1000
The adjacency comes back up now that both routers are using the same Key Chain to authenticate to each other:
Jun 5 20:52:46.091: %DUAL-5-NBRCHANGE: IP-EIGRP(0) 1000: Neighbor 192.168.100.2 (Serial0/0) is up: new adjacency
Next, lets turn on some debugging to verify that authentication is taking place:
R1#debug eigrp packets hello EIGRP Packets debugging is on (HELLO) R1# Jun 5 20:59:20.771: EIGRP: received packet with MD5 authentication, key id = 1
While we’re at it lets travel forward in time to July and see if Key 2 is being used:
Jul 1 21:07:20.927: EIGRP: received packet with MD5 authentication, key id = 2
Job done! Our EIGRP authentication is working as expected.
Thanks for reading.
Rich
Follow Rich on Twitter